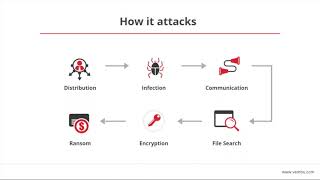
Media Summary: Check out this recorded webinar to know the latest trends and updates in In this video, Jermaine from Thales TCT demonstrates protecting AWS S3 buckets with AWS KMS vs Beyond Ransomware: Understanding Infostealer Attacks
Prevent Ransomware Attacks Simulated With Openssl Using Ciphertrust Transparent Encryption - Detailed Analysis & Overview
Check out this recorded webinar to know the latest trends and updates in In this video, Jermaine from Thales TCT demonstrates protecting AWS S3 buckets with AWS KMS vs Beyond Ransomware: Understanding Infostealer Attacks Join us in this podcast as Shrutirupa Banerjiee shares practical approaches and demonstrations of