Media Summary: Sophos Endpoint provides unparalleled defense against advanced cyberattacks. In this demonstration, we'll showcase a ... In our live session, we reviewed the necessary steps to ensure your business is protected from cyber threats, and demonstrated a ... When a receptionist receives a phishing email, the GRS Technology Solutions team steps in to block an attempted
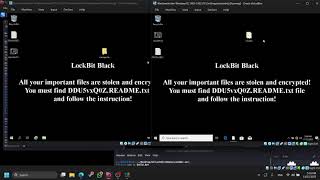
Ransomware Attack Simulation - Detailed Analysis & Overview
Sophos Endpoint provides unparalleled defense against advanced cyberattacks. In this demonstration, we'll showcase a ... In our live session, we reviewed the necessary steps to ensure your business is protected from cyber threats, and demonstrated a ... When a receptionist receives a phishing email, the GRS Technology Solutions team steps in to block an attempted ... there has been an estimated 20B worth of damages world-wide, due to Cybersecurity Expert Masters Program ... Two scenarios, one difference - can you spot it?
Cybersecurity Animation - How Ransomware Happens Part 1