Media Summary: Let's construct a public-key cryptosystem based on the computational hardness of Module-LWE. This is unlikely to be vulnerable ... Lattices are seemingly simple patterns of dots. But they are the basis for some seriously hard math Ready to become a certified watsonx AI Assistant Engineer? Register now and use code IBMTechYT20 for 20% off of your exam ...
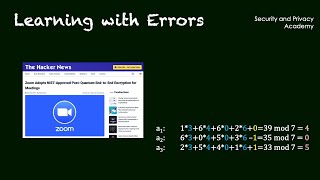
Post Quantum Cryptography Learning With Errors Da 2 - Detailed Analysis & Overview
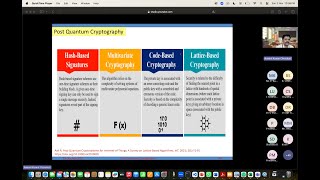
Let's construct a public-key cryptosystem based on the computational hardness of Module-LWE. This is unlikely to be vulnerable ... Lattices are seemingly simple patterns of dots. But they are the basis for some seriously hard math Ready to become a certified watsonx AI Assistant Engineer? Register now and use code IBMTechYT20 for 20% off of your exam ... Authors: Alexander Poremba (California Institute of Technology) ITCS - Innovations in Theoretical Computer Science. You can buy me a coffee if you want to support the channel: I explain This video is part of a module on lattice based
CIRM HYBRID EVENT Among the main candidates for What's the difference between quantum and THE CRISIS IS IMMINENT. Every password, every bank transaction, and every national secret protected by today's most trusted ... The wolfSSL team has long been aware of the threat of First paper ( On the Lattice Isomorphism Problem, Quadratic Forms, Remarkable Lattices, ... A talk by Alexander Poremba at the 14th Conference on the Theory of
Video lectures for Alfred Menezes's introductory course on the mathematics of lattice-based