Media Summary: Explain Important hints for arm arch V7 processors. Learn how to validate an STM32 application using a magic number and safely jump from a custom In this series we explore how to write a kernel from scratch. In this video we setup the transition between real and protected mode ...
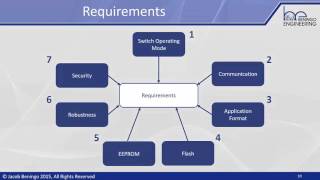
Part 2 Bootloader Design Considerations Security - Detailed Analysis & Overview
Explain Important hints for arm arch V7 processors. Learn how to validate an STM32 application using a magic number and safely jump from a custom In this series we explore how to write a kernel from scratch. In this video we setup the transition between real and protected mode ... This video quickly introduces one of the foundational enablers, Many embedded devices use complex boot sequences to initiate their operating systems. These boot chains often implement ...