Media Summary: Explain Important hints for arm arch V7 processors. Interrupts - Interrupt vector table - Startup code - NVIC. Learn how to validate an STM32 application using a magic number and safely jump from a custom
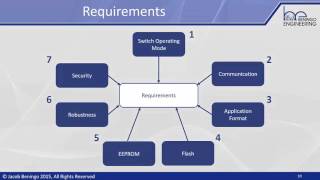
Part 2 Bootloader Design Consideration Invocation Rules - Detailed Analysis & Overview
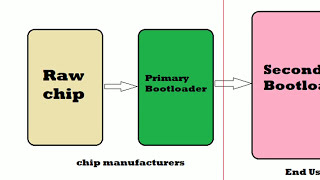
Explain Important hints for arm arch V7 processors. Interrupts - Interrupt vector table - Startup code - NVIC. Learn how to validate an STM32 application using a magic number and safely jump from a custom Embedded C for basically automotive engineers and embedded engineers. This is not a lecture series but discussion panel and ... In this series we explore how to write a kernel from scratch. In this video we setup the transition between real and protected mode ... I made a discord server for everyone interested in low level programming and malware. Check it out: ...
Learn about the definition of a security architecture, example attacks, and security measures to counter threats. Learn more ...