Media Summary: Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔ Solving format1 from exploit-exercises.com with a simple 7th video from the "Practical Buffer Overflow Exploitation" course covering the basics of Binary Exploitation. In this video we'll look ...
Microcorruption Ctf Format String Exploit Explained - Detailed Analysis & Overview
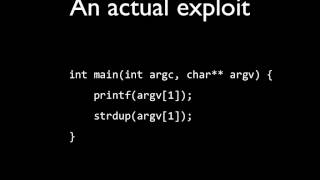
Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔ Solving format1 from exploit-exercises.com with a simple 7th video from the "Practical Buffer Overflow Exploitation" course covering the basics of Binary Exploitation. In this video we'll look ... In this episode we combine the last two videos. Solving Eat Sleep Pwn Repeat (ESPR - 150 pwn) challenge from the 33c3ctf. Dumping the binary through a You can follow me on instagram : Check out the
You can follow me on instagram : Amazing Challenge check it on the Welcome to another exciting walkthrough from MetaCTF April 2024! In this video, I dive into the world of Binary Exploitation with a ... ... and I'm going to give a brief introduction to using Welcome to 'Information Security 5 Secure Systems Engineering' course ! This lecture introduces