Media Summary: Hak5 -- Cyber Security Education, Inspiration, News & Community since 2005: Join Rob Fuller on this ethical hacking ... 7ASecurity offers training and penetration tests with a free fix verification -- get 40% off training with ... Pivoting & Port Forwarding Metasploit Red Team Tactics Network Pentesting CyberSecurity #
Meterpreter Pivoting - Detailed Analysis & Overview
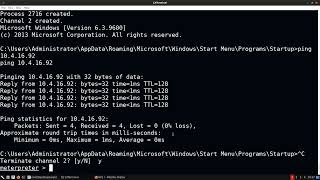
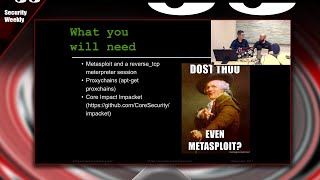
Hak5 -- Cyber Security Education, Inspiration, News & Community since 2005: Join Rob Fuller on this ethical hacking ... 7ASecurity offers training and penetration tests with a free fix verification -- get 40% off training with ... Pivoting & Port Forwarding Metasploit Red Team Tactics Network Pentesting CyberSecurity # Basic Pivoting Techniques: Metasploit Local Port Forwarding (through existing meterpreter session) NETWORK PIVOTING (Pivoting with the Metasploit Framework) Want to dominate network penetration testing? In this in-depth tutorial, I'll guide you through advanced
This video shows how to tunnel traffic through Beacon. You'll learn how to send the In this video The Ethical Hacking Guru shows you how to How to interact with the client system using Mis otras redes: En esta ocasión veremos como aprovechar las herramientas de Social Media ⭐ Discord: Twitter: Github: ... In this Tutorial we are going to exploit a vulnerable Jboss Apllication using the exploit "Jboss Invoke Deploy" and then using ...
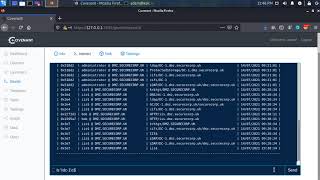
Basic Pivoting Techniques: Putting it all together (meterpreter and covenant)

![Pivoting In Metasploit - Metasploit Minute [Cyber Security Education]](https://i.ytimg.com/vi/MeSql-3aOsM/mqdefault.jpg)