Media Summary: In this Tutorial we are going to exploit a vulnerable Jboss Apllication Hak5 -- Cyber Security Education, Inspiration, News & Community since 2005: Join Rob Fuller on this ethical hacking ... Ad-hoc session working on pivoted packets through
Pivoting Using Meterpreter Metasploit - Detailed Analysis & Overview
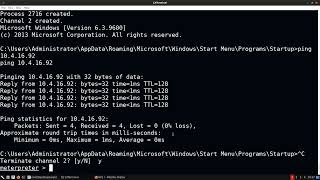
In this Tutorial we are going to exploit a vulnerable Jboss Apllication Hak5 -- Cyber Security Education, Inspiration, News & Community since 2005: Join Rob Fuller on this ethical hacking ... Ad-hoc session working on pivoted packets through Social Media ⭐ Discord: Twitter: Github: ... Basic Pivoting Techniques: Metasploit Local Port Forwarding (through existing meterpreter session) PortScanning Pivoting With Metasploit Post Exploitation
Right and for this one is another parameter we are أتمنى أنه عجبكم (أنا أخلي مسوؤليتي لأي ... Try out TryHackMe's Advent of Cyber! Today we're doing the 9th task (Dock the halls) where we do an intro to




![Pivoting In Metasploit - Metasploit Minute [Cyber Security Education]](https://i.ytimg.com/vi/MeSql-3aOsM/mqdefault.jpg)