Media Summary: Eduardo Showing how to apply the knowledge of our latest So today I'm gonna be talking about a I'll give you guys a little intro to A presentation by Benton Guess and Robert Dominguez for A&M's CSCE 451 Software Reverse Engineering taught by Dr. Liu.
Masterclass Emulation Vs Symbolic Execution - Detailed Analysis & Overview
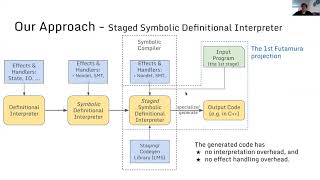
Eduardo Showing how to apply the knowledge of our latest So today I'm gonna be talking about a I'll give you guys a little intro to A presentation by Benton Guess and Robert Dominguez for A&M's CSCE 451 Software Reverse Engineering taught by Dr. Liu. Our engineering director Huck goes over how to use angr, a powerful tool to solve reverse engineering and binary exploitation ... The dual screen setup on Jannis' laptop was misbehaving. We've fixed the display of his slides and demo for the video. Episode 4 takes a deep, cinematic dive into the advanced architecture of an infection. We move beyond basic analysis to ...
Reverse engineering is a great way to learn about how computers work. Whether its malware analysis Missing video from March 2022 - Micah discusses Excel 4.0 (XL4) macros are a popular attack vector for threat actors, as security vendors struggle to play catchup and detect ... Hi, this is , a PhD student at working with , , and . MIT 6.858: Computer Systems Security Information about accessibility can be found at ... ... resource divider virtualization what's the fundamental difference and approach here
MIT 6.858 Computer Systems Security, Fall 2014 View the complete course: Instructor: Armando ...