Media Summary: In this workshop (2 hours), I explain how to use the tools (oledump, emldump, YARA rules, …) I developed to In this full series we will talk about Incident Response and it will be a Free Training Course for everyone. Today is Day-15 and I ... 0:00 Intro 1:50 md5 value of the file 2:10 VirusTotal 5:28 exiftool 7:44 strings 13:10 xorsearch You can access this course on ...
Malicious Document Analysis Docguard - Detailed Analysis & Overview
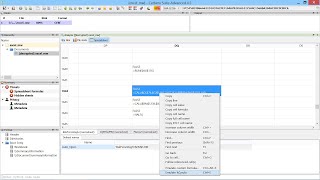
In this workshop (2 hours), I explain how to use the tools (oledump, emldump, YARA rules, …) I developed to In this full series we will talk about Incident Response and it will be a Free Training Course for everyone. Today is Day-15 and I ... 0:00 Intro 1:50 md5 value of the file 2:10 VirusTotal 5:28 exiftool 7:44 strings 13:10 xorsearch You can access this course on ... Dive into customizing FakeNet-NG's webroot to serve tailored content! FREE Serious About Learning CySec? Consider joining Hackaholics Anonymous. By ... In this video I solved the 1st Malware Challenge of LetsDefend, It's
This video shows how ThreatResponder is used to conduct a large-scale 0:00 Intro 2:00 olemeta 4:02 oleid 6:50 olevba You can access this course on LetsDefend for doing practice online: ... 0:00 Intro 0:17 Course content 0:45 Why should we worry about Microsoft Office