Media Summary: Updated video on Volatility 3 here: In this video we will use volatility framework to process an ... Join us in the Black Hills InfoSec Discord server here: to keep the security conversation going! So you think ... This presentation mainly focuses on the practical concept of
Live Forensics Memory Analysis - Detailed Analysis & Overview
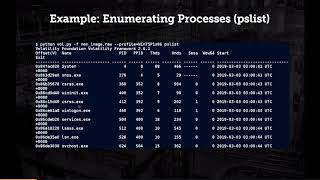
Updated video on Volatility 3 here: In this video we will use volatility framework to process an ... Join us in the Black Hills InfoSec Discord server here: to keep the security conversation going! So you think ... This presentation mainly focuses on the practical concept of - Go further into blue teaming with our associate-level course, SOC 101! It's accompanied by a ... In this video, we show how to conduct a low-level Sponsor a Video: Pentests & Security Consulting: Get Trained: ...
You're likely familiar with many tools that allow us to capture In this hands-on guide, discover how to perform