Media Summary: You're likely familiar with many tools that allow us to In this episode, we'll take a look at a quick and easy way to find the Intermediate Symbol File (ISF) for the In this hands-on guide, discover how to perform live
Linux Memory Forensics Memory Capture And Analysis - Detailed Analysis & Overview
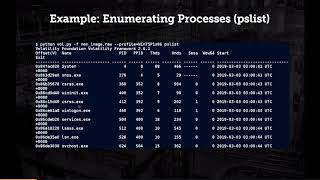
You're likely familiar with many tools that allow us to In this episode, we'll take a look at a quick and easy way to find the Intermediate Symbol File (ISF) for the In this hands-on guide, discover how to perform live In this video we will use LiME to acquire an image of physical 00:00 - Intro 00:47 - Discovering a weird binary running in /tmp/ but it doesn't exist on disk 01:55 - Start of explaining dd copying ... Continuing our Blue Team Training series, will cover the importance of
In this video, we show you how to install This presentation mainly focuses on the practical concept of



![How to Use LiME to Take a RAM Dump of a Linux Machine | Memory Forensics Tutorial [Hindi]](https://i.ytimg.com/vi/j1AzBCNTMOs/mqdefault.jpg)