Media Summary: In this video tutorial, we discuss the important concept of the Abroad Education Channel : Company Specific HR Mock ... Link for playlists: Link for our website: ...
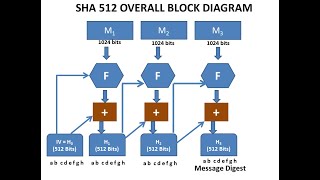
Lecture 31 Sha 512 Cryptographic Hash Function - Detailed Analysis & Overview
In this video tutorial, we discuss the important concept of the Abroad Education Channel : Company Specific HR Mock ... Link for playlists: Link for our website: ... Myself Shridhar Mankar a Engineer l YouTuber l Educational Blogger l Educator l Podcaster. My Aim- To Make Engineering ... Course : B.C.A Semester : V SEM Subject : NETWORK SECURITY Chapter Name : In this video, we dive into the fascinating world of