Media Summary: Learn to develop modern malware and more BYOVD techniques with Maldev Academy! The Intel vPro® platform helps mitigate low-level Yeah you said when uh creating your database you would only use the latest version of the
Kernel Exploitation Via Vulnerable Drivers - Detailed Analysis & Overview
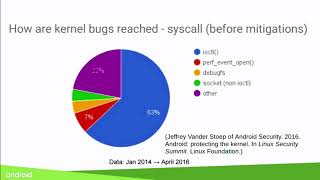
Learn to develop modern malware and more BYOVD techniques with Maldev Academy! The Intel vPro® platform helps mitigate low-level Yeah you said when uh creating your database you would only use the latest version of the As the rest of the Android security infrastructure improves, the Android/Linux In this video, I demonstrate Windows privilege escalation using changing protected process and hiding process BYOVD : Rootkit Development for Red team Operations
Hi all I've started to create this video series on LOLDrivers: Mike Haag: The HTA Generator will be released and in a public ... Though many security mechanisms are deployed in Apple's macOS and iOS systems, some old-fashioned or poor-quality