Media Summary: changing protected process and hiding process BYOVD : Rootkit Development for Red team Operations Exploiting the signed ... The Intel vPro® platform helps mitigate low-level exploitation! See how the Intel vPro® platform helps you ... Massive thank you to Snyk for sponsoring this video! HEVD
Kernel Driver Vulnerabilities At T Threattraq - Detailed Analysis & Overview
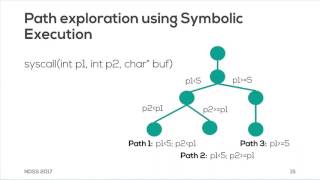
changing protected process and hiding process BYOVD : Rootkit Development for Red team Operations Exploiting the signed ... The Intel vPro® platform helps mitigate low-level exploitation! See how the Intel vPro® platform helps you ... Massive thank you to Snyk for sponsoring this video! HEVD Yeah you said when uh creating your database you would only use the latest version of the With the continuous upgrade by Microsoft, the latest windows 10 version has become more and more powerful and supports more ... Video taken during the Network and Distributed System Security (NDSS) Symposium 2017, held February 26 through March 1, ...
Jianfeng Pan, Guanglu Yan, and Xiaocao Fan, IceSword Lab, 360 Internet Security Center Discovering Dive into the fascinating world of static reverse engineering Windows Learn to develop modern malware and more BYOVD techniques with Maldev Academy! In early 2021, an external researcher reported to Google three lines of code indicating the xt_qtaguid