Media Summary: This video steps through the architecture of In this video, I dive deep into the formation of Start learning cybersecurity with CBT Nuggets. In this video, Keith Barker covers the five essential ...
Ipsec Ike Phase 1 Ike Phase 2 - Detailed Analysis & Overview
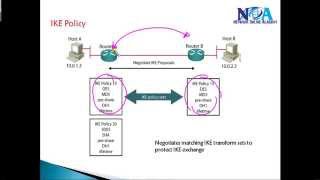
This video steps through the architecture of In this video, I dive deep into the formation of Start learning cybersecurity with CBT Nuggets. In this video, Keith Barker covers the five essential ... Visit for a free 30 day trial. The first 200 people will get 20% off their annual premium subscription. ... inside of which we can negotiate the formation of the 𝗬𝗼𝘂 𝘄𝗶𝗹𝗹 𝗹𝗲𝗮𝗿𝗻 𝗦𝗶𝘁𝗲-𝘁𝗼-𝗦𝗶𝘁𝗲 𝗩𝗣𝗡 𝗙𝘂𝗻𝗱𝗮𝗺𝗲𝗻𝘁𝗮𝗹𝘀 𝗮𝗻𝗱 𝘂𝗻𝗱𝗲𝗿𝘀𝘁𝗮𝗻𝗱 𝗵𝗼𝘄 𝗮𝗻 𝗜𝗣𝗦𝗲𝗰 𝗩𝗣𝗡 𝘄𝗼𝗿𝗸𝘀 𝗯𝗲𝘁𝘄𝗲𝗲𝗻 𝘁𝘄𝗼 𝗱𝗶𝗳𝗳𝗲𝗿𝗲𝗻𝘁 𝗻𝗲𝘁𝘄𝗼𝗿𝗸𝘀. 𝗧𝗵𝗶𝘀 ...
This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... A secure network starts with a strong security policy that defines the freedom of access to information and dictates the deployment ... Abroad Education Channel : Company Specific HR Mock ... Start learning cybersecurity with CBT Nuggets. In this video, CBT Nuggets trainer Keith Barker takes ...