Media Summary: A secure network starts with a strong security policy that defines the freedom of access to information and dictates the deployment ... Start learning cybersecurity with CBT Nuggets. In this video, Keith Barker covers the five essential ... In this video, I dive deep into the formation of
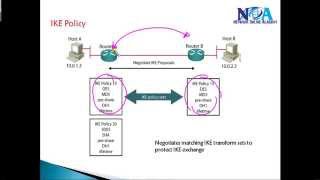
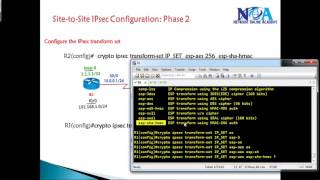
Ccie Routing Switching Version 5 Ipsec Ike Phase 1 - Detailed Analysis & Overview
A secure network starts with a strong security policy that defines the freedom of access to information and dictates the deployment ... Start learning cybersecurity with CBT Nuggets. In this video, Keith Barker covers the five essential ... In this video, I dive deep into the formation of