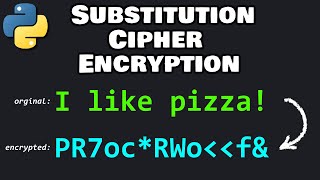
Media Summary: Image Encryption using visual cryptography-IEEE paper demo Thapar University Patiala Software Engineering Project. python import random import string chars = " " + string.punctuation + string.digits + string.ascii_letters chars ...
Image Encryption And Decryption System - Detailed Analysis & Overview
Image Encryption using visual cryptography-IEEE paper demo Thapar University Patiala Software Engineering Project. python import random import string chars = " " + string.punctuation + string.digits + string.ascii_letters chars ... Get a look at our course on data science and AI here: This is the project for the design and development of software named as “Secure This video tutorial explains the purpose of
In 1997, a contest began to develop a new The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ...