Media Summary: HackRich In this video I discussed how printf function works, what is Solving format1 from exploit-exercises.com with a simple In this episode we combine the last two videos.
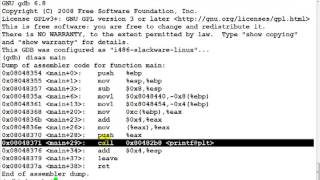
Format String Vulnerability Leak Content From The Stack - Detailed Analysis & Overview
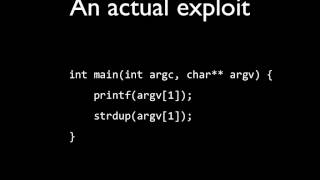
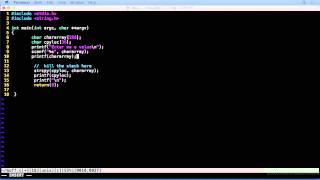
HackRich In this video I discussed how printf function works, what is Solving format1 from exploit-exercises.com with a simple In this episode we combine the last two videos. In this video I have discussed what format strings are, how they are used, and what are 7th video from the "Practical Buffer Overflow Exploitation" course covering the basics of Binary Exploitation. In this video we'll look ... Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔
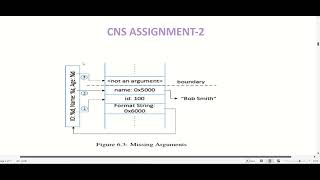
Hello hackers today we're going to be talking about format strings and HackRich File Used:- In this video I have discussed ... Hi there! This video introduces the core ideas behind Format String Vulnerabilities Primer Part 4 Viewing the Stack ... what if our format string buffer is sitting on the Ments remember when printf is called what it expects is the
07 03 Hacking and Penetration - Format String Attacks Welcome to 'Information Security 5 Secure Systems Engineering' course ! This lecture introduces