Media Summary: FTK Imager Download: Kaggle_Notebook: ... We all know that there are many applications which can detect malware but not This presentation mainly focuses on the practical concept of
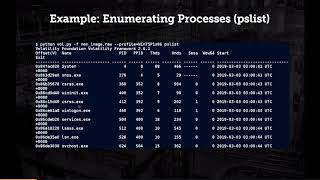
Fileless Malware Analysis Using Memory Forensic Tools - Detailed Analysis & Overview
FTK Imager Download: Kaggle_Notebook: ... We all know that there are many applications which can detect malware but not This presentation mainly focuses on the practical concept of Ben and Alex uncover the stealthy world of Integrate ANY.RUN solutions into your company: Make security research and dynamic The extra sneaky, camouflaged malware variant known as