Media Summary: This presentation mainly focuses on the practical concept of Episode 6 is a fast-paced, action-oriented lecture designed for senior Download the pcap here and follow along: https://
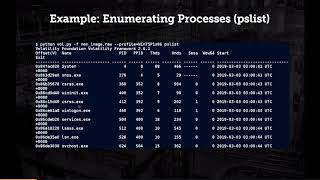
A Simple Process To Analyse Malware Samples With Memory Forensics - Detailed Analysis & Overview
This presentation mainly focuses on the practical concept of Episode 6 is a fast-paced, action-oriented lecture designed for senior Download the pcap here and follow along: https:// CyberSecurity In this video I am going to show, how to In this video, we dive into the basics of Find your next cybersecurity career! CySec Careers is the premiere platform designed to connect candidates ...
We all know that there are many applications which can detect Episode 5 – Everyday Cyber Podcast In this episode, Alex Reid explores how