Media Summary: CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... Want To Know What Is DAC? This Video Explains The Concept Of
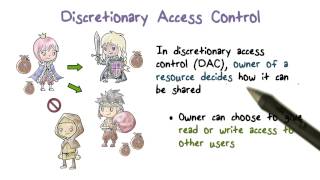
Discretionary Access Control - Detailed Analysis & Overview
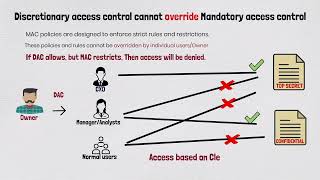
CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... Want To Know What Is DAC? This Video Explains The Concept Of In this session, we break down one of the most critical topics in cybersecurity — I continue the discussion about access control. In this video, I introduce the general concept of a Get the threat intelligence guide → Learn about the technology → Exploring the ...
In this video, you'll learn about least privilege, Discretionary Access Control on Grant Revoke Oracle Failure Types Database Important Questions 👉 Follow us on Social ...











![Android 12 Internals: [Ch2.vid2] Discretionary Access Control (DAC) in the Linux Kernel](https://i.ytimg.com/vi/oBi-OGFQ_9k/mqdefault.jpg)


