Media Summary: In this video, we cover the theory behind In Today's Video, Alex will guide you on how to exploit Shodan Dork: http.title:"Zyxel NAS542" --------------------------------------------------------------- Linkedin: ...
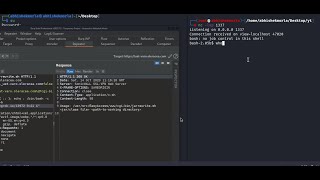
Day 18 Command Injection Bugbounty Ethicalhacking - Detailed Analysis & Overview
In this video, we cover the theory behind In Today's Video, Alex will guide you on how to exploit Shodan Dork: http.title:"Zyxel NAS542" --------------------------------------------------------------- Linkedin: ... In this video, I demonstrate how command injection vulnerabilities allow attackers to execute system commands on a vulnerable ... CyberSecurity Basics: Watch other POC's Videos: ... In the theme settings function of a web application, a dangerous loophole exists where any file can be uploaded without ...








![[Hindi] Command Injection - Full Tutorial | Learn Command Injection Bug in 30 Minutes #bugbounty](https://i.ytimg.com/vi/HZPdrRQtx_U/mqdefault.jpg)

![Day-18 - XSS/Cross Site Scripting Vulnerability Part 1 - Bug Bounty Free Course [Hindi]](https://i.ytimg.com/vi/tZKF0LnPVsA/mqdefault.jpg)




