Media Summary: In this video, we cover the theory behind Think your input filters are safe? In this video, we go beyond the semicolon to explore how Mehmet INCE is a Managing Partner of INVICTUS. He regularly shares his ideas about current security issues and offers his ...
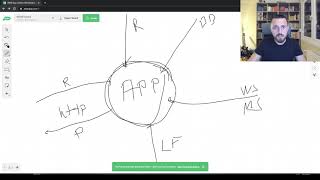
Command Injection Complete Guide - Detailed Analysis & Overview
In this video, we cover the theory behind Think your input filters are safe? In this video, we go beyond the semicolon to explore how Mehmet INCE is a Managing Partner of INVICTUS. He regularly shares his ideas about current security issues and offers his ... Is your password for sale on the Dark Web? Find out now with Dashlane: (Use code ... In this ethical hacking tutorial, we explore the Dear Defronixters !! This is the 32nd Class of our Bug Bounty
Educational Purposes Only, Teaching Cyber Security to others with passion! Stay updated with the latest features and ... Welcome to another exciting episode from Cyberwings Security! Unleashing the Power of












![Day-32 Command Injection Vulnerability - Bug Bounty Free Course [Hindi]](https://i.ytimg.com/vi/ZhYsfqQdSmU/mqdefault.jpg)

![Command Injection [Shell Injection] | Beginner's Guide to Web Security #8](https://i.ytimg.com/vi/Bienhrrk31M/mqdefault.jpg)
