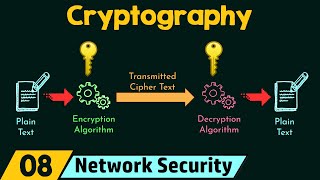
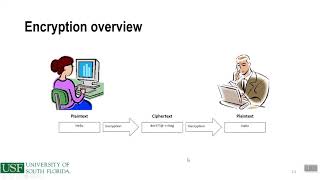
Media Summary: In this video, I have covered the basics of Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter: Animation ... Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ...
Cryptographic Control And Encryption Policy Walkthrough - Detailed Analysis & Overview
In this video, I have covered the basics of Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter: Animation ... Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... Michigan - Applied Generative AI Specialization ...






![27-[5.20] SOC2 – Cryptographic/ Encryption Policy](https://i.ytimg.com/vi/2DxE5UiO3JA/mqdefault.jpg)