Media Summary: In this video, we explain Cloud Security in Cloud Computing in a simple and clear way. This is Cloud Computing In this video, Prof. Alex O. Akpodiete from Atawa AI breaks down RSA (Rivest–Shamir–Adleman) is an algorithm used to
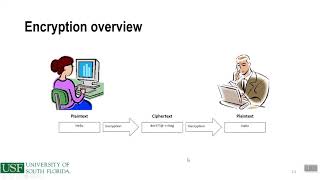
Chapter 7 Encryption Controls - Detailed Analysis & Overview
In this video, we explain Cloud Security in Cloud Computing in a simple and clear way. This is Cloud Computing In this video, Prof. Alex O. Akpodiete from Atawa AI breaks down RSA (Rivest–Shamir–Adleman) is an algorithm used to Network Security Threats, Malware, Spyware, SQL injection, Firewalls, Anti-virus, Phishing. In this lesson, you will be learnt how to secure all the passwords that display in the configuration by In this lecture, we're going to begin our exploration of
How do you protect your organization's most valuable asset without stifling the business? This video summarizes