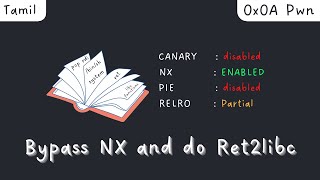
Media Summary: That's the English version about this topic where I manually adjust the gadgets into the memory in order to Nope okay I will move on so for exercise one I want you guys to just uh MOST VIDEOS ARE UNDER THE LIVE SECTION! In this video I walk through an example of return oriented
Bypass Dep Protection Using Rop Chain Execute Shellcode With Mona Py - Detailed Analysis & Overview
That's the English version about this topic where I manually adjust the gadgets into the memory in order to Nope okay I will move on so for exercise one I want you guys to just uh MOST VIDEOS ARE UNDER THE LIVE SECTION! In this video I walk through an example of return oriented In this video walk-through, we covered another scenario of exploiting a binary vulnerable to buffer overflow. This scenario ... That´s the second version about the subject where I manually adjust the gadgets into the memory in order to execute ... When it comes to exploit development for Microsoft Windows,
This is the second video continuing through the freely available Corelan Tutorials! More specifically, in this video we will be ...