Media Summary: Making yourself the all-powerful "Root" super-user on a computer using a Team 6 (Jonathan Ojeda / Santiago Cabrieles) Hello Everyone. In this video I am going to tell you about
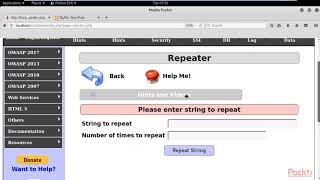
Buffer Overflow Attack 22vv1a1242 - Detailed Analysis & Overview
Making yourself the all-powerful "Root" super-user on a computer using a Team 6 (Jonathan Ojeda / Santiago Cabrieles) Hello Everyone. In this video I am going to tell you about Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔ This tutorial goes over the basic technique of how to exploit a Buffer overflows are not only inconvenient, but dangerous too.
buffer overflow buffer overflow attack in cyber security, cyber security tutorial cs 503 what is buffer overflow attack ... We updated this video for accuracy and improved graphics. Please view the new version here: This video tutorial has been taken from Web Security. You can learn more and buy the full video course here ...