Media Summary: Find your next cybersecurity career! CySec Careers is the premiere platform designed to connect candidates ... In this video, we dive into the powerful capabilities of the In this video, we show you how to install
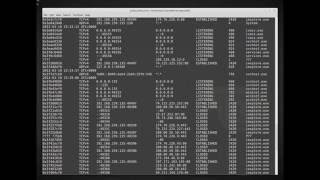
Analyze Memory Using Volatility Tool In Kali Linux - Detailed Analysis & Overview
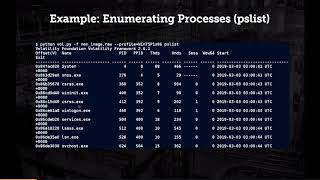
Find your next cybersecurity career! CySec Careers is the premiere platform designed to connect candidates ... In this video, we dive into the powerful capabilities of the In this video, we show you how to install ... class so as you can see this is your known image and I'm going to run This presentation mainly focuses on the practical concept of In this video I will guide you how to setup your own
The video provides a detailed overview of Welcome to **Cyberhawk Consultancy**, where we turn complex digital Continuing our Blue Team Training series, will cover the importance of