Media Summary: Find your next cybersecurity career! CySec Careers is the premiere platform designed to connect candidates ... ... class so as you can see this is your known image and I'm going to Burp Suite Deep Dive course: Recon in Cybersecurity course: Python Basics ...
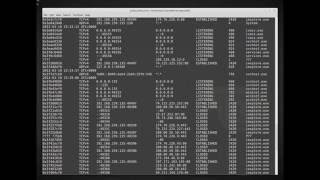
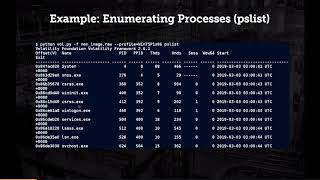
Ethical Hacking Dfir Lab Memory Dump Analysis Using Volatility To Perform Memory Analysis - Detailed Analysis & Overview
Find your next cybersecurity career! CySec Careers is the premiere platform designed to connect candidates ... ... class so as you can see this is your known image and I'm going to Burp Suite Deep Dive course: Recon in Cybersecurity course: Python Basics ... In this session we explain important files and concepts when getting started Room Link ------- Receive video documentation ... This presentation mainly focuses on the practical concept of
A sluggish DMZ system raised suspicion but internal teams found nothing. Now it's our turn to investigate, and all we have to go ...