Media Summary: Disclaimer This video is made available for educational and informational purposes only. We believe that everyone must be ... Making yourself the all-powerful "Root" super-user on a computer using a The best to write code that is safe is to first break code that is not safe. Today, we'll be taking the code that I wrote for my strings ...
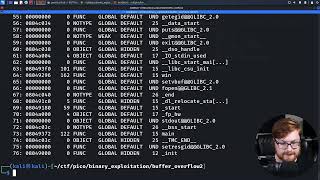
56 Running A Buffer Overflow Attack Computerphile Buffer Overflow Basic Buffer Overflow - Detailed Analysis & Overview
Disclaimer This video is made available for educational and informational purposes only. We believe that everyone must be ... Making yourself the all-powerful "Root" super-user on a computer using a The best to write code that is safe is to first break code that is not safe. Today, we'll be taking the code that I wrote for my strings ... PS, jump into the HackTheBox Cyber Apocalypse CTF! Help the channel grow with a ... Hello Everyone. In this video I am going to tell you about buffer overflow buffer overflow attack in cyber security, cyber security tutorial cs 503 what is buffer overflow attack ...