Media Summary: Making yourself the all-powerful "Root" super-user on a computer using a We updated this video for accuracy and improved graphics. Please view the new version here: This tutorial goes over the basic technique of how to exploit a
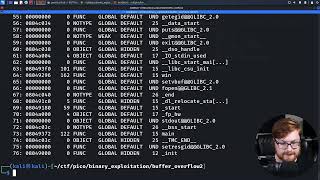
2 Running A Buffer Overflow Attack Computerphile Why Do Buffers Overflow - Detailed Analysis & Overview
Making yourself the all-powerful "Root" super-user on a computer using a We updated this video for accuracy and improved graphics. Please view the new version here: This tutorial goes over the basic technique of how to exploit a Security+ Training Course Index: Professor Messer's Course Notes: ... The second episode in a series covering x86 stack Hello Everyone. In this video I am going to tell you about
Solving stack6 from exploit-exercises.com with the re2libc technique. stack6: PS, jump into the HackTheBox Cyber Apocalypse CTF! Help the channel grow with a ...