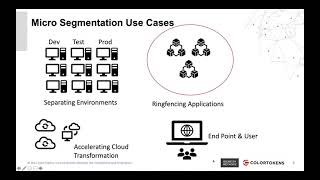
Media Summary: Learn about current threats: Learn about IBM Illumio Core - Zero Trust Micro-Segmentation
Zero Trust Micro Segmentation Explained Etciso Secufest Insights - Detailed Analysis & Overview
Learn about current threats: Learn about IBM Illumio Core - Zero Trust Micro-Segmentation