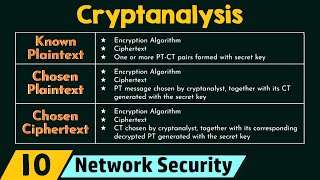
Media Summary: Ever wondered how hackers break encryption codes? This video explains the term New Zealand's cute infosec con (& book publishers) ✨ Live Stream VOD from Kawaiicon III (6th - 8th ... ... were used to generate the ciphertext this is what we call
What Is Cryptanalysis - Detailed Analysis & Overview
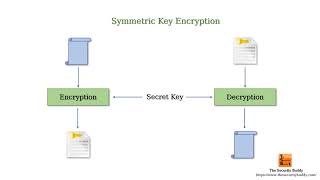
Ever wondered how hackers break encryption codes? This video explains the term New Zealand's cute infosec con (& book publishers) ✨ Live Stream VOD from Kawaiicon III (6th - 8th ... ... were used to generate the ciphertext this is what we call Bear with me as I learn to use a new video editing software. In this video I start with the very basics, so some of you probably ... Network Security: Cryptography – Key Terms Topics discussed: 1) Introduction to cryptography and the role of cryptography in ... In this tutorial we will learn cryptography in easy methods with examples. if this video is helpfull to you please like and ...
additimeline " L I K E " " C O M M E N T ✍ " " S HA R E ✌ " "S U B S C R I B E " "B E L L " This Video is For Helping People ... Today we're going to talk about how to keep information secret, and this isn't a new goal. From as early as Julius Caesar's Caesar ... This video explains what cryptology, cryptography, and Definitions, historical ciphers and their







![What is Cryptology | Cryptography and Cryptanalysis? | Mr-Zee [ IT LEARNING HUB ]](https://i.ytimg.com/vi/XDdNYht6y7U/mqdefault.jpg)