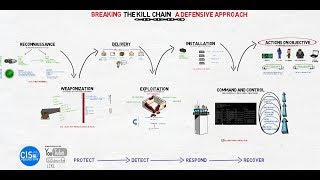
Media Summary: Cyber attacks don't happen randomly - they follow a pattern. In this video, we explain the In this video walk-through, we practically explained the Hi Guys! Thank you for watching this video! We hope this video was helpful about learning about the
Weaponization Cyber Kill Chain - Detailed Analysis & Overview
Cyber attacks don't happen randomly - they follow a pattern. In this video, we explain the In this video walk-through, we practically explained the Hi Guys! Thank you for watching this video! We hope this video was helpful about learning about the Join us in this comprehensive YouTube video as we delve into the intricacies of the Get insight into core Cybersecurity themes in our “ In this video we will be learning What is
For more than a decade, Lockheed Martin's Intelligence Driven Defense and Join this channel to get access to perks: ... What if you could break down every cyberattack into just seven stages? In this video, Frank Downs walks through the Free Cram Course To Help Pass your SY0-601 Security+ Exam. If you are Preparing/Planning to take your SY0-601 CompTIA ... Hi everyone! In this video I walk you through the second step of the