Media Summary: Video 5 : Attify Android Security and Exploitation Course : Setting basic pentest environment Video 3 : Attify Android Security and Exploitation Course : Application Signing Basics Video 4 : Attify Android Security and Exploitation Course) : Extracting certificate information
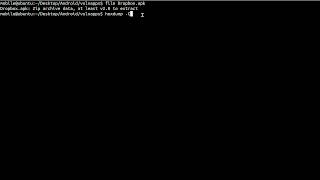
Video 5 Attify Android Security And Exploitation Course Setting Basic Pentest Environment - Detailed Analysis & Overview
Video 5 : Attify Android Security and Exploitation Course : Setting basic pentest environment Video 3 : Attify Android Security and Exploitation Course : Application Signing Basics Video 4 : Attify Android Security and Exploitation Course) : Extracting certificate information