Media Summary: Paper by Rishab Goyal, Satyanarayana Vusirikala presented at Crypto 2020 See ... In light of security challenges that have emerged in a world with complex networks and cloud computing, the notion of functional ... Your private messages deserve real protection. WhatsApp's end-to-end
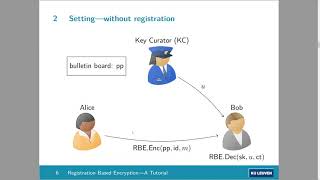
Verifiable Registration Based Encryption - Detailed Analysis & Overview
Paper by Rishab Goyal, Satyanarayana Vusirikala presented at Crypto 2020 See ... In light of security challenges that have emerged in a world with complex networks and cloud computing, the notion of functional ... Your private messages deserve real protection. WhatsApp's end-to-end Paper by Alexandre Bois, Ignacio Cascudo, Dario Fiore, Dongwoo Kim presented at PKC 2021 See ... A look at all things decentralized identity and Transform your coding skills with this Educational File Encryptor GUI, built using Python + Tkinter + PyCryptodome (AES).
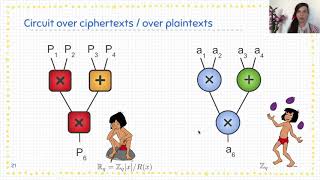
Paper by Dario Fiore, Anca Nitulescu, David Pointcheval presented at PKC 2020 See ... In this video, I endeavored to explain digital signatures in one minute, making it as quick and easy as possible. Exciting developments are happening in the Web3 social space, and to build the envisioned metaverse, it's important to have the ...