Media Summary: DeepReflect: Discovering Malicious Functionality through Binary Reconstruction Evan Downing, Georgia Institute of Technology; ... The Circle Of Life: A Large-Scale Study of The IoT Michelle Y. Wong University of Toronto Abstract:
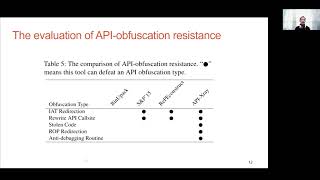
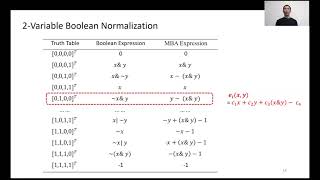
Usenix Security 21 Obfuscation Resilient Executable Payload Extraction From Packed Malware - Detailed Analysis & Overview
DeepReflect: Discovering Malicious Functionality through Binary Reconstruction Evan Downing, Georgia Institute of Technology; ... The Circle Of Life: A Large-Scale Study of The IoT Michelle Y. Wong University of Toronto Abstract: WebWitness: Investigating, Categorizing, and Mitigating