Media Summary: Indistinguishability Obfuscation and UCEs: The Case of Computationally
Unpredictability Applied Cryptography - Detailed Analysis & Overview
Indistinguishability Obfuscation and UCEs: The Case of Computationally
Media Summary: Indistinguishability Obfuscation and UCEs: The Case of Computationally
Indistinguishability Obfuscation and UCEs: The Case of Computationally

This video is part of an online course,
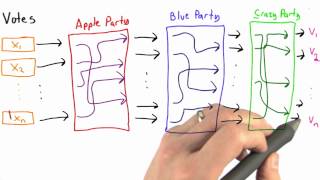
This video is part of an online course,

This video is part of an online course,

This video is part of an online course,

This video is part of an online course,

Cryptography

Indistinguishability Obfuscation and UCEs: The Case of Computationally