Media Summary: Understand and explore common red teaming Introduce some of the Windows and AD attacks that can be used to obtain the hashes. Kerberoasting ... Tutorial room exploring some basic file-upload vulnerabilities in websites 🏷️🏷️ Room Link: ...
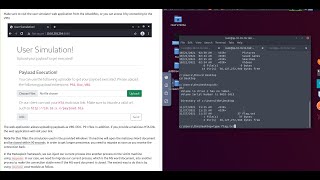
Tryhackme Weaponization Task 9 - Detailed Analysis & Overview
Understand and explore common red teaming Introduce some of the Windows and AD attacks that can be used to obtain the hashes. Kerberoasting ... Tutorial room exploring some basic file-upload vulnerabilities in websites 🏷️🏷️ Room Link: ... This is the continuation of our Red Team Path. This is a very entry level and great way to start learning red teaming! This is a box ... Follow me on Twitter: Join my community discord server: In this video walk-through, we practically explained the
Hi, Learning to hide malicious scripts inside unharmed files is advantageous.Especially when you follow the foot prints of a Cyber ... Commands in comment section Like and Subscribe Follow me on LinkedIn Learn how a vulnerability evolves and methods to weaponize multiple vulnerabilities leading to RCE. This is a walkthrough of the Shells Overview room from