Media Summary: This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... In this video I explain what the open-source software called "
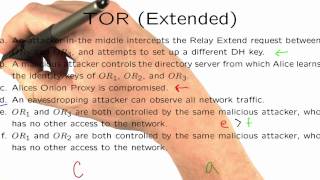
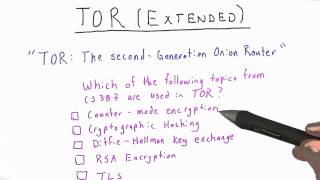
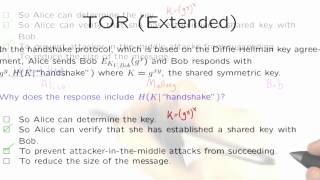
Tor Applied Cryptography - Detailed Analysis & Overview
This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... In this video I explain what the open-source software called "