Media Summary: Presented by Kenan O'Neal at IstioCon 2022. Quick dive for beginners on IstioCon2021 Presented at IstioCon 2021 by Sam Stoelinga. So you've actually done security well and are using an external ... To get better at system design, subscribe to our weekly newsletter: Checkout our bestselling System Design ...
Tls Origination Best Practices - Detailed Analysis & Overview
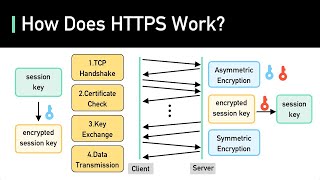
Presented by Kenan O'Neal at IstioCon 2022. Quick dive for beginners on IstioCon2021 Presented at IstioCon 2021 by Sam Stoelinga. So you've actually done security well and are using an external ... To get better at system design, subscribe to our weekly newsletter: Checkout our bestselling System Design ... Proactive website and SSL certificate monitoring: ... Ivan Ristic, Director of Engineering at Qualys, talks about SSL Labs and their efforts to understand how SSL was used and to ... In this video, we explore mTLS (Mutual Transport Layer Security) and why it's a critical tool for securing communications where ...
One of the key operational challenges of securing microservices is understanding, securing and monitoring access to external ... Get a Free System Design Roadmap PDF with 145 pages by subscribing to our monthly newsletter: ... Welcome to Kubernetes Class 3 where you can achieve 25+ LPA In this class, we cover production-style Kubernetes setup ... Welcome to day 20/40 of the Certified Kubernetes Administrator (CKA) series! In this video, we will try to understand how SSL/ Become a senior software engineer with a job guarantee: Learn how ...