Media Summary: Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter: Animation ... Weekly system design newsletter: Checkout our bestselling System Design Interview books: Volume 1: ... Download the guide: Cybersecurity in the era of GenAI → Learn more about the technology ...
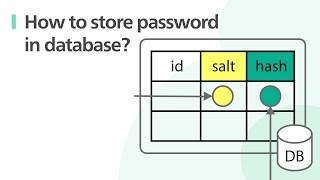
The Proper Way To Secure Your Databases - Detailed Analysis & Overview
Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter: Animation ... Weekly system design newsletter: Checkout our bestselling System Design Interview books: Volume 1: ... Download the guide: Cybersecurity in the era of GenAI → Learn more about the technology ... Follow for more Kotlin & Android tips! ... In this short, A bar chart race showcases the top DBMS from 2012 to 2025, based on their popularity. The DB-Engines Ranking ... Ready to become a certified Administrator -
SML (SecretMemoryLocker) is a deterministic password generator that redefines Learn essential data privacy techniques to