Media Summary: Telegram group : contact me on Gmail at shraavyareddy810.com contact me on ... Myself Shridhar Mankar a Engineer l YouTuber l Educational Blogger l Educator l Podcaster. My Aim- To Make Engineering ... Link for playlists: Link for our website: ...
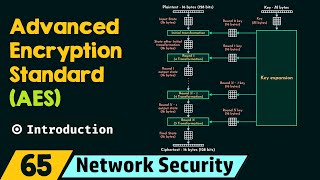
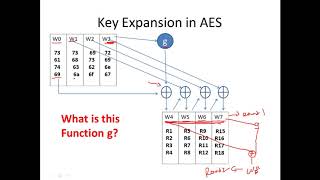
Sub Byte Function In Aes Advanced Encryption Standard - Detailed Analysis & Overview
Telegram group : contact me on Gmail at shraavyareddy810.com contact me on ... Myself Shridhar Mankar a Engineer l YouTuber l Educational Blogger l Educator l Podcaster. My Aim- To Make Engineering ... Link for playlists: Link for our website: ... In this lecture we will be looking at the following concepts mentioned below 1. Block Diagram for In 1997, a contest began to develop a new encryption algorithm to become the THIS VIDEO COVERS BLOCK DIAGRAM AND TRANSFORMATIONS PERFORMED ON