Media Summary: A growing number of compliance mandates require sensitive It's time to set the record straight about By taking advantage of features provided in release
Streamlining Data Encryption While Maintaining Ibm I Availability - Detailed Analysis & Overview
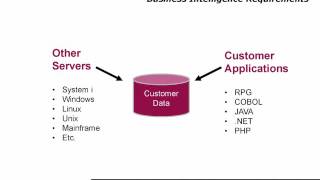
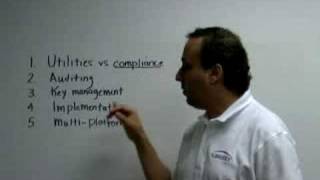
A growing number of compliance mandates require sensitive It's time to set the record straight about By taking advantage of features provided in release DB2 Field Procedures (FieldProcs) were introduced in Sensitive information needs to be kept secret. That's an indisputable fact for modern organizations, where sensitive information ... nuBridges on the Top 5 critical elements of
The continuous news of personal information stolen from major retailers and financial institutions have driven consumers and ... Ready to become a certified Architect - Cloud Pak for Is your organization using legacy programs or unsecured processes to transfer files on the











![[WEBINAR] Encryption for IBM i by Raz-Lee Security](https://i.ytimg.com/vi/k6yHgs1Yr6I/mqdefault.jpg)




