Media Summary: In this video we'll be exploring how to attack, detect and defend against the theft of Big thank you to ThreatLocker for sponsoring my trip to ZTW25 and also for sponsoring this video. To start your free trial with ... Educational Purpose Only ⚠️ In this video, you'll learn how hackers can hijack browser
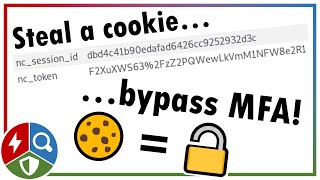
Stealing Web Session Cookies To Bypass Mfa Credential Access - Detailed Analysis & Overview
In this video we'll be exploring how to attack, detect and defend against the theft of Big thank you to ThreatLocker for sponsoring my trip to ZTW25 and also for sponsoring this video. To start your free trial with ... Educational Purpose Only ⚠️ In this video, you'll learn how hackers can hijack browser Sign up for DeleteMe! Use the coupon code SNUBS for 20% off any consumer plans! Linky: We explore how sophisticated tools like Evilginx exploit vulnerabilities to steal Adversary-in-the-Middle (AitM) attacks are one of the most dangerous ways threat actors
PlexTrac makes pentest reporting a breeze -- try their premiere reporting & collaborative platform: ... Think your accounts are safe because you have a strong password and 2FA? Think again. In this video, we dive into the world of ... Stealing an O365 cookie from Edge to "bypass" authentication and 2FA










![[HINDI] All about Sessions and Cookies | Cookie Stealing and Session Hijacking | Website Hacking #10](https://i.ytimg.com/vi/4TgijmwFSXA/mqdefault.jpg)





