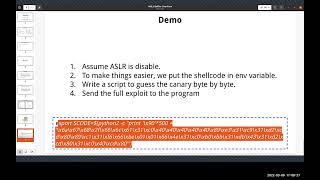
Media Summary: Affiliated Course: Presented by: Michiel Lemmens Follow me here: 10th video from the "Practical Buffer Overflow Exploitation" course covering the basics of Binary Exploitation. NX and This video is part of the Udacity course "Intro to Information Security". Watch the full course at ...
Stack Canaries Gingerly Sidestepping The Cage - Detailed Analysis & Overview
Affiliated Course: Presented by: Michiel Lemmens Follow me here: 10th video from the "Practical Buffer Overflow Exploitation" course covering the basics of Binary Exploitation. NX and This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... Keep on learning with Brilliant at Get started for free, and hurry — the first 200 people get ... View the full free MOOC at This class is for C/C++ developers learning secure development, and ... Let's learn about a great mitigation against
- Managed by the official OWASP Media Project ... Discussing basic memory protections like bounds-checking functions, non-executable stacks, In this video, BCI instructor Jeremy Blackthorne uses Ghidra to reverse-engineer a binary exploitation challenge with a Welcome to 'Information Security 5 Secure Systems Engineering' course ! This lecture discusses techniques for preventing buffer ... In this tutorial, we will explore a defense mechanism against stack overflows, namely the 4th Pwn video from 's 1337UP LIVE CTF 2022: "Bird". We have a printf() format vuln and a buffer overflow this time but it's ...
MonSec Week 11 Workshop ran on 1/06/2020 presented by Rafael Hermann. Rafi provides an overview of
















![Bypassing Stack Canaries and NX/DEP (Ret2Lib-C) - Bird - [Intigriti 1337UP LIVE CTF 2022]](https://i.ytimg.com/vi/XaWlKYgmEDs/mqdefault.jpg)
