Media Summary: Two huge security issues found in almost all modern processors. How do they work and what can we do about it? Let's find out! Squarespace link: Visit and use offer code TECHQUICKIE to save 10% off your first order. Why it's a bad idea to build a Virtual Private Network using TCP. Dr Steve Bagley on TCP over TCP...
Spectre Meltdown Computerphile - Detailed Analysis & Overview
Two huge security issues found in almost all modern processors. How do they work and what can we do about it? Let's find out! Squarespace link: Visit and use offer code TECHQUICKIE to save 10% off your first order. Why it's a bad idea to build a Virtual Private Network using TCP. Dr Steve Bagley on TCP over TCP... Over the past decades, security has been largely regarded as a software developer's responsibility, while hardware vendors have ... Another year, another security breach that could expose all of your information. Installing updates might be a good New Year's ... Making yourself the all-powerful "Root" super-user on a computer using a buffer overflow attack. Assistant Professor Dr Mike ...
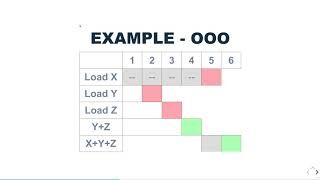
A presentation on my understanding of the Extracting a secret key by simply watching the flickering of an LED? Sounds implausible but that's what we're discussing with Dr ... The Port Smash exploits Hyperthreading and timings to work out what other programs are doing. Dr Steve Bagley looks at how. Why does my neighbour hear the score in the big game before I do? Dr Steve Bagley looks at why video streams suffer delays. Wanacrypt works super fast and even when you're offline. Dr Pound explains how hybrid ransomware systems work. Original ... Gentle overview of the core ideas exploited by the