Media Summary: TuxHouse is an Educational community wich aims to teach people about Linux, Blockchain, Android && Cybersecurity using the ... In this video, we break down one of the most dangerous beginner mistakes in Solidity: using Become an in-demand blockchain MASTER: CODE: ...
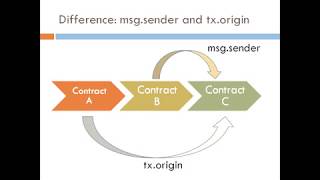
Smart Contract Hacking 0x0f Simple Tx Origin Vs Msg Sender Example - Detailed Analysis & Overview
TuxHouse is an Educational community wich aims to teach people about Linux, Blockchain, Android && Cybersecurity using the ... In this video, we break down one of the most dangerous beginner mistakes in Solidity: using Become an in-demand blockchain MASTER: CODE: ... FREE TRAININGS (WEB3 DEV, FLASH LOANS...) How to find your first 6-Figures Blockchain Developer Job: ... Recorded at WASTC FDW Summer 2022 More info: Ep 100: an example of tx origin attack in smart contract
Phishing is a cyber attack where the attacker disguises as a trusty-worthy entity and tricks an user into doing something harmful. Exploiting an often over looked programming error, that leads to the Nesta aula veremos como utilizar os objetos