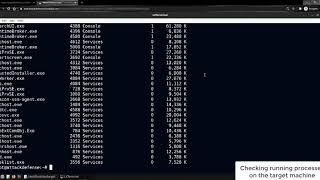
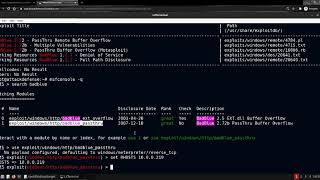
Media Summary: Learn how to manage remote devices in your environment with Target Server is running an insecure application, which is vulnerable to Buffer Overflow. In this lab, you will learn in the ... Links and Resources Mentioned in the Video: Thank you for watching this video! Join my Discord server: ...
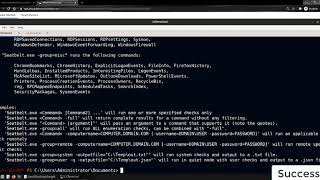
Services Exploitation Winrm Powershell Remoting From Linux - Detailed Analysis & Overview
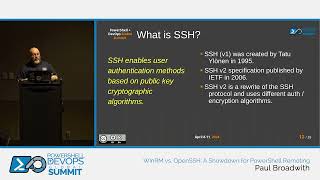
Learn how to manage remote devices in your environment with Target Server is running an insecure application, which is vulnerable to Buffer Overflow. In this lab, you will learn in the ... Links and Resources Mentioned in the Video: Thank you for watching this video! Join my Discord server: ... Welcome to our beginner-friendly tutorial on In this session, we dive into the comparison between In this lab we will take a look at the steps to Enable
SSH, or Secure Shell is one of the most essential tools for anyone working with